New SAML Authentication Plugin for Development Projects
TL;DR
- SAML remains the mandatory security standard for Fortune 500 enterprise contracts.
- Manual SAML implementation costs roughly 200 engineering hours and risks security vulnerabilities.
- Better Auth v1.3 plugin enables TypeScript-native SSO integration in under an hour.
- Automated tools handle XML canonicalization, certificate rotation, and multi-tenant provisioning.
- Enterprise 'Identity-as-Code' replaces legacy SOAP and XML manual coding struggles.
SAML in 2026: Stop Building It Yourself (The "Better Auth" Guide)
SAML is the toll booth on the highway to enterprise revenue.
Let's be honest: developers hate it. We universally prefer the clean, predictable JSON of OIDC. But 78% of Fortune 500 companies don't care about our preferences. They mandate Security Assertion Markup Language (SAML) to unlock their contracts.
For years, landing an enterprise deal meant wrestling with "XML hell," deciphering cryptic SOAP errors, and patching libraries that hadn't seen a commit since 2022.
That ends now. The shift toward "Identity-as-Code" has produced the Better Auth v1.3 SSO Plugin. It’s a TypeScript-native solution that turns a three-month engineering slog into a predictable, hour-long task.
If you are building B2B SaaS in 2026, you don't need to understand the intricacies of XML canonicalization. You just need a plugin that handles the dirty work for you. Here is how to bypass the "SAML Tax" and implement robust, multi-tenant SSO without losing your mind.
Why is SAML Still a Thing?
It is easy to dismiss SAML as a dinosaur. But in the enterprise world, dinosaurs still rule the earth.
Large organizations refuse to adopt social logins or pure OIDC for one specific reason: The Kill Switch.
They need to provision—and more importantly, de-provision—thousands of employees instantly across hundreds of apps from a single dashboard. Usually Okta, Microsoft Entra ID (formerly Azure AD), or JumpCloud. When an employee gets fired, IT hits one button, and access is revoked everywhere. Instantly.
Think of SAML implementation not as a feature request, but as a "tax" required to enter the market. If your app cannot consume a SAML assertion, you simply cannot close the deal with a hospital, a bank, or a government agency. They won't change their security policy for your startup; you have to adapt to their infrastructure.
For a broader look at what enterprises demand beyond just SSO, read our guide to enterprise authentication, which breaks down the full compliance stack.
Build vs. Buy: The 200-Hour Trap
The most dangerous phrase in a developer's vocabulary is, "I'll just build a quick SAML handler myself."
Don't do it.
On the surface, it looks like a simple POST request. It isn't. In reality, a secure implementation requires handling XML parsing (notorious for vulnerabilities), certificate rotation logic, clock skew adjustments, and replay attack prevention. Industry data suggests that building a production-grade SAML service from scratch takes approximately 200 engineering hours.
And that’s before you factor in the maintenance nightmare when a library dependency breaks.
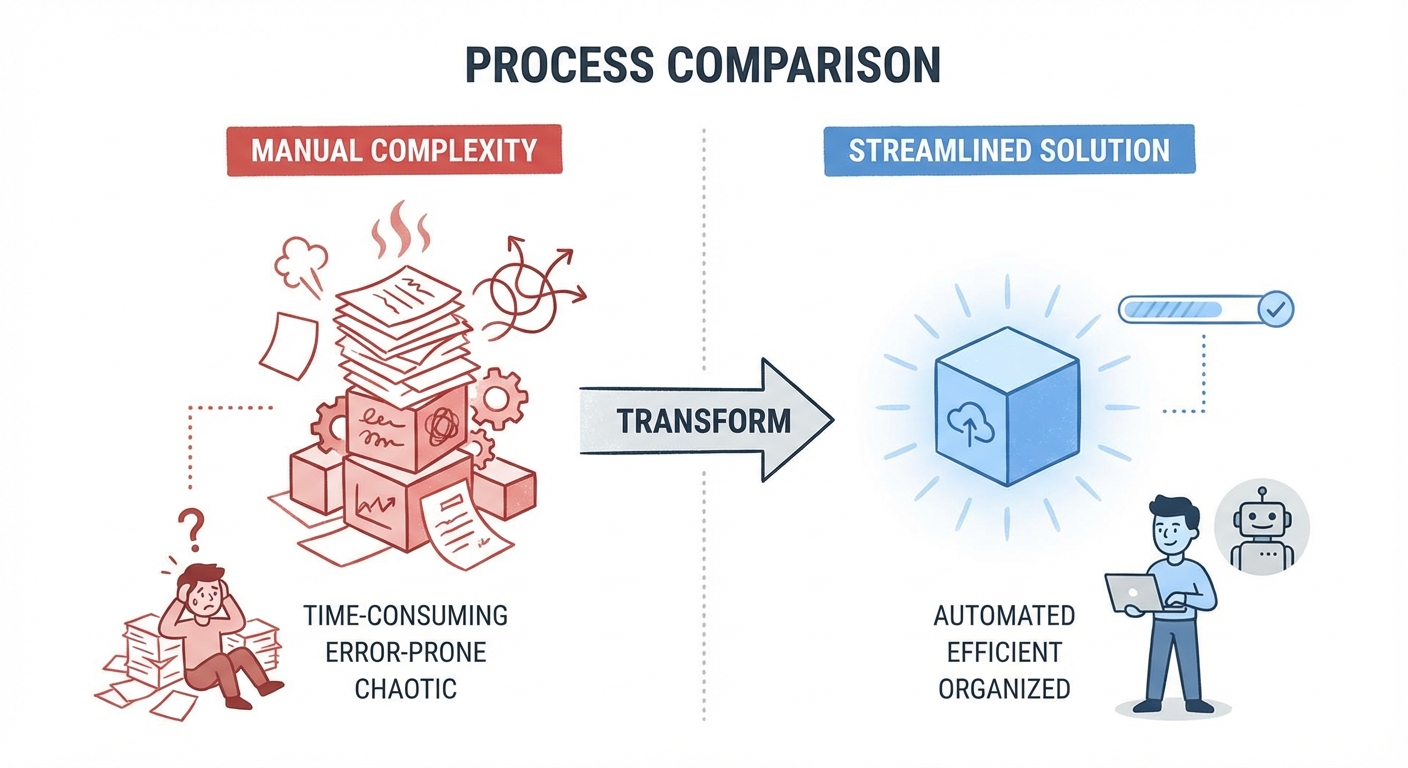
One look at the 80-page OASIS SAML 2.0 Standard usually convinces developers that this is not a wheel worth reinventing. The specification is dense, pedantic, and unforgiving. A single whitespace error in your XML signature validation can leave your application wide open to spoofing.
By utilizing a dedicated plugin, you are effectively "buying" those 200 hours back for the cost of a simple configuration file.
Technical Deep Dive: Under the Hood of "Better Auth"
The new wave of authentication plugins hits different.
Legacy libraries like Passport-SAML were built for a callback-heavy Node.js era. The Better Auth SSO plugin is built TypeScript-first. It relies on strict typing to prevent configuration errors before you even run the code.
The architecture functions as a middleware layer. It sits between your application routes and the raw incoming request, intercepting the SAML POST data before it touches your business logic. It abstracts the XML exchange entirely, converting the encrypted assertion into a clean, typed user object.
You can review the specific API methods in the Better Auth Documentation, but the core philosophy is "configuration over implementation." You define who the provider is, and the plugin handles how the handshake happens.
Visualizing the Handshake
To understand what the plugin is automating, we need to visualize the flow. In an SP-Initiated (Service Provider) flow, your application acts as the traffic cop, directing the user to their corporate login page and verifying their ID upon return.
Implementation Guide: The Multi-Tenant Nightmare
The biggest hurdle in B2B SaaS is multi-tenancy. You aren't just connecting to one Identity Provider; you are connecting to hundreds.
Customer A uses Okta. Customer B uses Google Workspace. Customer C uses a custom ADFS setup from 2016.
Hardcoding credentials in an .env file is impossible here. You need a dynamic schema.
The Better Auth plugin solves this by allowing you to store configuration details (Metadata URL, Entry Point, Certificate) in your database, linked to a specific tenantId. When a user tries to log in, the plugin fetches the specific configuration for that organization on the fly.
This approach integrates seamlessly with other tools in your stack—see our developer tools overview for examples of how to pipe this identity data into your analytics or CRM.
Security "Gotchas": Avoiding the Golden SAML Trap
SAML is powerful, but it is also fragile.
High-profile attacks like "Golden SAML" and XML Signature Wrapping have taken down massive networks. These attacks exploit parsers that don't strictly validate where the signature is placed within the XML tree.
The advantage of using a modern plugin is that these checks are default behavior, not optional configurations. The Better Auth plugin enforces:
- Strict Signature Validation: It ensures the signature covers the entire assertion, preventing wrapping attacks.
- Replay Attack Prevention: It checks the
NotBeforeandNotOnOrAftertimestamps. If an attacker intercepts a token and tries to use it 10 minutes later, the door remains locked. - Audience Restriction: It verifies that the token was intended specifically for your app, not another service.
Security is paramount; ensure your chosen plugin adheres to the OWASP SAML Security guidelines to prevent accidentally leaving doors open. SAML is just one layer of your defense; verify your full stack against our SaaS security checklist to ensure you aren't vulnerable elsewhere.
Handling IdP-Initiated Flows (The Enterprise Curveball)
Here is the scenario that breaks most home-grown implementations:
The user doesn't visit your website. Instead, they wake up, log into their corporate Okta dashboard, and click the icon for your app.
This is called an IdP-Initiated Flow. There is no prior request from your server. No session state to check against. You just receive a POST request out of the blue containing a user's identity.
Strict validation is even more critical here because you cannot verify the request against a pre-existing transaction ID. The plugin must distinguish between a valid unsolicited response and a potential attack.
Conclusion: Future-Proofing Your Identity Stack
We are all waiting for the day when OIDC completely replaces SAML. But that day is not coming in 2026. The legacy infrastructure of the enterprise world moves slowly.
However, the tools we use to interface with that infrastructure have evolved rapidly.
You no longer need to be an XML expert to sell to the Fortune 500. By migrating to a schema-based plugin like Better Auth, you secure your application against sophisticated attacks and free up your engineering team to build features that actually differentiate your product.
Audit your current auth stack today. If you see manual XML parsing code, delete it.
FAQ
Q: Why use a SAML plugin instead of a managed service like Auth0? A: Money and control. Managed services often charge per "Enterprise Connection" (which can cost thousands per month). A plugin like Better Auth keeps the infrastructure in your code and the data in your database, usually for free or a fraction of the cost.
Q: Does this plugin support IdP-initiated login? A: Yes. This is non-negotiable for enterprise compatibility, as many employees access apps directly via their corporate dashboards (like the Microsoft My Apps portal).
Q: Can I support multiple Identity Providers for different customers? A: Absolutely. This is "Multi-Tenant SSO." The plugin lets you store configuration details dynamically for each tenant. Tenant A connects to Okta, Tenant B connects to Google Workspace. No code changes required.
Q: Is this compatible with Next.js and Node.js backends? A: Yes. The Better Auth plugin is framework-agnostic but optimized for modern TypeScript environments, making it ideal for Next.js, Express, or Fastify backends.